Dynamic Blocking List
Instead of typing manually in firewall (create an object, add it to block list object, commit, etc) here is easier way of blocking ip addresses as well as URLs in PAN firewall, OS version 7.x and up (i believe it works for lower OS versions but i have no test bed to confirm).
Some of the malicious IP addresses are related to following bulletin:
This Malware Analysis Report (MAR) is the result of analytic efforts between the Department of Homeland Security (DHS) and the Federal Bureau of Investigation (FBI). Working with U.S. Government partners, DHS and FBI identified Trojan malware variants used by the North Korean government. This malware variant is known as TYPEFRAME. The U.S. Government refers to malicious cyber activity by the North Korean government as HIDDEN COBRA.
Here are steps to accomplish this:
- Build a simple web server (all default settings are fine)
- Create a text file and place it in default web directory (this text file will be updated with new IP address entries, just keep adding them on the bottom of the list)
- Use “External Dynamic List” object from firewall to create a new Dynamic object. In the object you will enter url for a new web site (something like this):
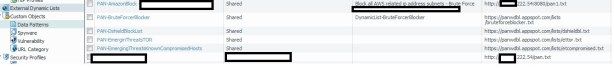
As you can see I have two web sites: http://x.x.222.54/pan.txt and http://x.x.222.54:8080/pan1.txt or more.
One web is used to block IP addresses as per different security bulletins and second web is used to block ip addresses specific for Azure AWS (we had some attacks attempts from AWS IP addresses).
You can build new website for different blocking purposes (one to block URL, another to block IPs, another to block someone who bothers you at the work 🙂 etc.) that will be distinguished with different port number.
- Setup External Dynamic List to update itself every 5 min.
- Call this dynamic list from firewall block rule. Use External Dynamic list object as a source (PAN-Amazon….)

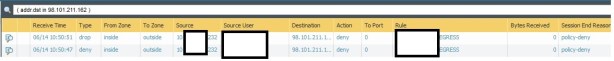
And here are results:
Here is my web structure:

Here is my text file:

So, you can setup a block rule, start pinging one of blocked IP (for testing ping should be allowed) and watch how ping gets dropped after firewall updates its rule after 5 min.