DNS Sinkholing with PAN
Setting up a DNS sinkholing is very simplified with PAN firewall. If you are in security you probably know about DNS sinkholing; if you are not in this line of work, let me quickly explain what is all about… DNS Sinkholing is a mechanism aimed to protect users by intercepting DNS request to resolve URL to IP address and ultimately to prevent users connecting to malicious domains. This is achieved by returning a false IP address to client that is requesting domain name resolution for malicious domain. The IP address returned to the client is one defined and easily identified by administrator or PAN’ default DNS sinkholing IP address of 71.19.152.112
The idea behind DNS sinkholing is the same regardless if you are using external (like OpenDNS) or internal DNS server.
So, how can we do this?
Separate sinkholing security zone should be created on firewall, not necessary but easier to setup firewall rules when you use sinkhole zone.
Firewall rule is created to drop traffic destined to Sinkhole IP address, in my case it will be 1.1.1.1. An IP object has been created, called PAN-Sinkhole-IP
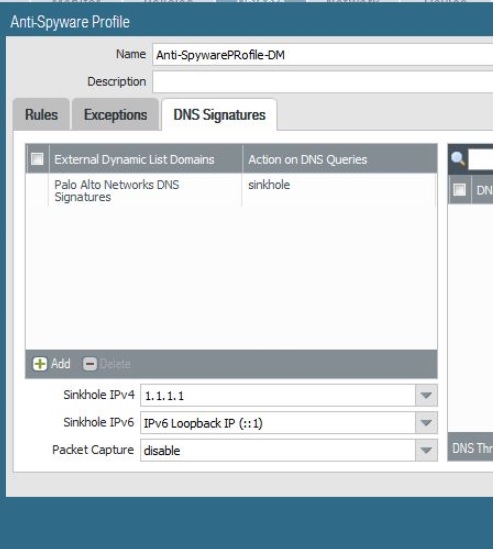
 Sinkhole has been enabled and sinkhole IP address entered:
Sinkhole has been enabled and sinkhole IP address entered:
Ok, all is setup. So, how can i test it then?
The easiest way is to make active one of the older antivirus signature updates, then open release notes for the latest antivirus signature update and look for one Suspicious DNS Query, like for example uroninau.website
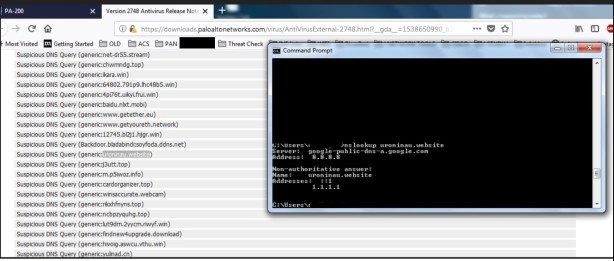
The nslookup query returns PAN’ configured sinkhole IP address of 1.1.1.1.
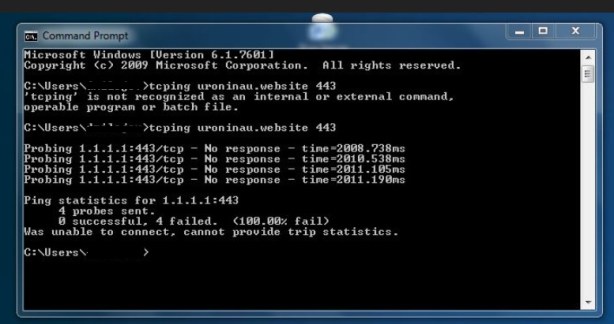
Now, simulating traffic to malicious domain shows that PAN sinkhole IP address returns response. The actual traffic will never be able to reach malicious domain since this traffic will be directed to PAN’ sinkhole IP address – client received “wrong” ip address for malicious domain as part of nslookup
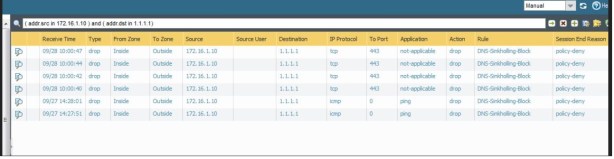
The firewall monitoring tab shows denied traffic..
.. and report can be built to show all internal computers trying to reach malicious domain.

The realtime alerting can be setup as well; for this purpose i have setup a syslog server to receive an syslog alert when internal user trying to reach 1.1.1.1

That should do the trick…